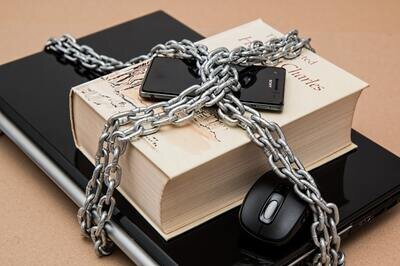
Has Mobile HR Data Access Reduced the Security of Our HR Systems?
Mobile HRMS data is a popular feature both with managers and employees these days. Being able to find out employee details and perform transactions while on the go, what’s not to like? There is a worry, however, are all of these mobile HR data applications safe? In particular, as it often involves sensitive employee data such social security number, birthdate, compensation, etc. the stakes can be higher if something potentially goes wrong. What should you think about with mobile HRMS and security?
with HRMS mobile, you’re opening yourself up to bigger issues if an employee is incorrectly granted mobile access or the wrong level of employee data
First, it’s important to remember that there are mobile applications in use for both personal and business reasons that contain confidential data such as banking details and credit card numbers. Mobile HR applications have joined a tried and true platform of security measures and procedures such as multi-level security (having to enter multiple passwords through secure sites), encryption and minimum standards for the mobile devices accessing the network.
Second, we’ve all heard the usual scare stories about an employee forgetting an unlocked phone just before boarding a plane, etc. but if anything, employee awareness about data security is much higher that it was prior to these devices being commonly used. An employee security policy is no longer a static document lost on a shared drive but instead, employees are applying the same security behavior and best practices that they apply to their devices when using personal sites, such as when they access their bank via mobile and transfer money. That being said, it’s always a good idea to have a policy in place to wipe any device that is reported missing or stolen to further alleviate any risks to HR data.
Recommended Read: HRMS Vendor Guide - Find HRMS vendors offering a secure mobile HRMS platform
Security access also comes into play when mobile HR is involved. While it may be a minimal risk if Joe from Training (previously an HR Administrator) still has access to the HRMS from his desk computer due to old security configurations, it becomes a different story when Joe has this access via mobile. Security reviews could previously afford to be a little sloppy or late with little repercussion, but now with HRMS mobile, you’re opening yourself up to bigger issues if an employee is incorrectly granted mobile access or the wrong level of employee data. In the case of mobile HRMS, follow the ‘least access needed to do the job’ principle and you’ll always be a winner when the auditors come calling.
Free white paper

HRMS Software Pricing Guide
Get your comprehensive guide to the cost of HRMS software.

Free white paper

HRMS Software Vendor Directory
Put the most up-to-date HRMS vendor directory on your desk today! Nearly 100 vendors listed.

Related articles
-

4 HR functions that work better on mobile
While all HR transactions at one stage were performed without mobile devices the benefits utilizi...
-

Which features should your mobile HRMS app prioritize?
A guide to the features your HRMS mobile app should make as accessible as possible
-
Six basic HR data security threats in 2026
Read about the most common threats to HR data security and how to combat them.

